
CYBER SYRUP
Delivering the sweetest insights on cybersecurity.
The AI Insights Every Decision Maker Needs
You control budgets, manage pipelines, and make decisions, but you still have trouble keeping up with everything going on in AI. If that sounds like you, don’t worry, you’re not alone – and The Deep View is here to help.
This free, 5-minute-long daily newsletter covers everything you need to know about AI. The biggest developments, the most pressing issues, and how companies from Google and Meta to the hottest startups are using it to reshape their businesses… it’s all broken down for you each and every morning into easy-to-digest snippets.
If you want to up your AI knowledge and stay on the forefront of the industry, you can subscribe to The Deep View right here (it’s free!).
Bloody Wolf APT Uses Legitimate Tools to Breach Government Targets
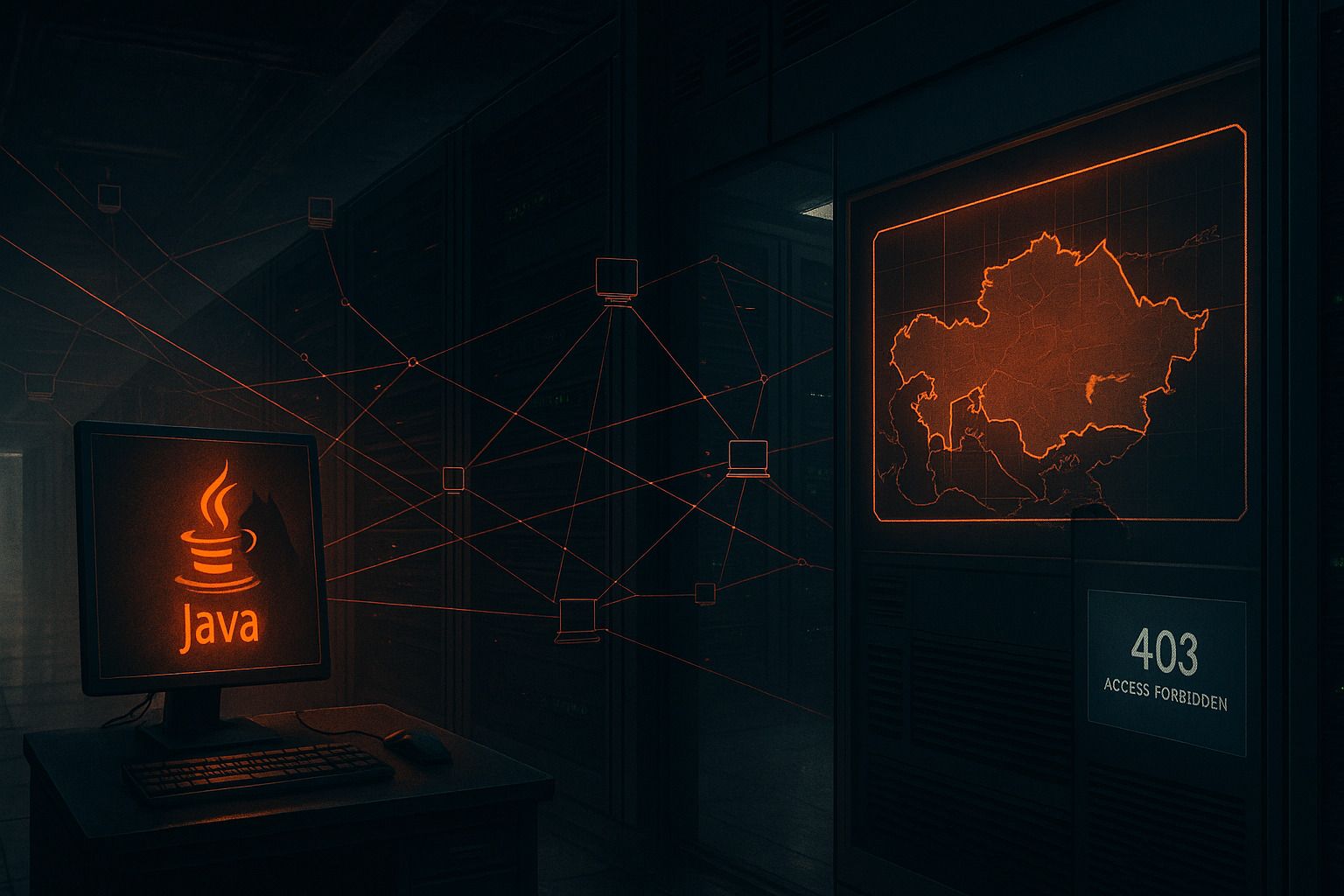
A newly identified cyber campaign led by the Bloody Wolf APT group is leveraging legitimate remote-access tools, rather than traditional malware, to infiltrate government organizations across Central Asia. The operation uses social engineering, Java-based loaders, and older versions of NetSupport RAT to quietly establish persistent access, highlighting a continued shift toward low-cost, low-visibility tactics.
Context
Since late 2023, the Bloody Wolf threat group has been refining its methods, moving away from custom malware and toward trusted software already common in enterprise environments. This shift makes detection harder and blends malicious activity into normal system behavior.
Group-IB and UKUK conducted a joint investigation into the campaign, which has expanded beyond initial targets in Kyrgyzstan to new activity in Uzbekistan as of 2025.
What Happened
Researchers discovered a sustained APT campaign deploying malicious Java Archive (JAR) files disguised as government case documents. These lures impersonate ministries of justice and instruct recipients to install Java to view legal materials.
Once executed, the loader installs an older version of NetSupport Manager—legitimate remote-administration software often misused by threat actors—to gain remote access and control of victim systems.
The attackers have tailored their infrastructure to specific regions. In Uzbekistan, the malicious domains use geofencing to deliver harmful downloads only to local users while redirecting all other traffic to legitimate government websites.
Technical Breakdown
Delivery and Social Engineering
Attackers impersonate government agencies with spoofed documents and domains.
Victims are tricked into downloading Java-based loaders disguised as legal case files.
Short, credible lure messages reinforce legitimacy.
Loader Functionality
The Java 8–based loaders are intentionally simple:
Contain a single class and no obfuscation
Fetch NetSupport binaries over HTTP
Establish persistence via autorun entries and scheduled tasks
Display bogus error messages to reduce suspicion
Include a launch-limit counter (set to 3) to limit execution and evade detection
Attackers also use an automated JAR generator that creates numerous variants with customized registry entries, file paths, and decoy messages.
Command and Control
NetSupport Manager (2013 version) provides remote shell, file operations, and system control
Publicly available licenses reduce traceability
Infrastructure relies on spoofed domains and geofencing to segment victims
Loaders download components dynamically over HTTP
Impact Analysis
This campaign enables:
Persistent remote access to sensitive government systems
Credential theft and data collection
Continuous monitoring and command execution
Low-visibility operations that evade traditional malware indicators
The use of legitimate tools dramatically reduces detection rates, especially in environments lacking behavioral analytics.
Why It Matters
This operation represents a broader trend:
APT groups increasingly leverage legitimate remote-access software to hide in plain sight.
Social engineering remains the primary entry vector, even for advanced actors.
Low-cost, modular toolchains allow sustained espionage activities without bespoke malware.
Governments and critical institutions must strengthen monitoring of administrative tools—not only traditional malware.
Expert Commentary
Group-IB researchers note that Bloody Wolf’s use of simple Java loaders combined with NetSupport RAT reflects a strategic shift: “The combination of social engineering and accessible tooling enables the group to remain effective while keeping a low operational profile.”
They warn that Central Asian institutions should prepare for continued spear-phishing campaigns and iterative adaptations of this infection chain.
Key Takeaways
Bloody Wolf APT is expanding its operations across Central Asia.
Attackers use legitimate tools (NetSupport RAT) instead of custom malware.
Java-based loaders provide stealthy installation and persistence.
Geofenced infrastructure selectively targets regional victims.
Social engineering and document impersonation remain highly effective.
Monitoring legitimate IT tools is now essential for defense.

